If you’re working with any business that is auditing its data, there are probably a few features you’ve found yourself using over and over again. SQL Server Audit is one critical example that’s been showing up in data auditing for quite some time now. But what you probably don’t know is that Office 365 has its own set of features to make your life a lot easier.
Office 365 Auditing pulls signals from everywhere inside the service, and uses intelligence to keep you updated with activities in your organization. It can help you learn if a user has purged a document, if an admin mingled permissions and privileges, what actions your users took in the last few days, or any other activity you can imagine.
This article will help you make the most of auditing and of the alerts that you can set up within your cloud service. This auditing capability is an option for all Office 365 tenants, but only the most popular enterprise subscriptions, E3 and E5, come with it standard.
1) What content is being audited?
Here’s a list of the data that can be audited inside an Office 365 tenant:
- Exchange: Admin activity, end-user (mailbox) activity.
- OneDrive: Admin activities, file activity.
- SharePoint: File activity, sharing activity.
- Security and Compliance Center: Admin activity.
- Azure Active Directory: O365 logins, directory activities.
- Power BI: Admin activities.
You can see that quite a lot of information is collected, but Microsoft is working to increase the auditing scope further, so the list will get even longer. Some of these are enabled by default, like the admin activities in Exchange Online, but others, like the mailbox activities, must be turned on manually.
You don’t have to use the Office 365 embedded application to interpret or use the collected data. You can install the Management Activity API to get the data out and use it as you wish, like feeding it into other third-party applications. You can choose from 300+ applications from Microsoft partners that use the API.
2) Audit Logging in Office 365 – Unified
Why unified? Because now you can search the logs of the entire service spectrum in one go. From SharePoint to Azure AD, you get all the logs bundled together, and you’re able to query them inside the Security & Compliance Admin Center (S&CC) in Office 365.
Remember first to turn on audit logging by clicking on the Start recording user and admin activity option in the Audit log search page. If this option is missing, it means either that auditing has already been enabled for your organization, or Microsoft turned it on for everyone (as was their plan at the time of writing).
All unified audit log entries are kept for 90 days. Note that it can take up to 24 hours after an event occurs for it to be shown in an audit query.
3) Search the audit log
You can easily tap into the security and compliance features of your tenant; just follow this link, which drops you directly into the S&CC: https://protection.office.com. From there, go to Search and Investigation and Search audit log. There you will find various options to set up and initiate your audit search.
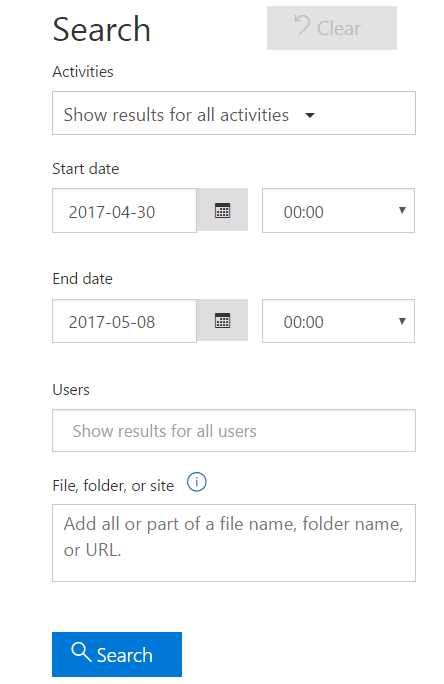
When the log gets really big, select only certain activities that you want to investigate instead of keeping all of them (like most of us are doing). The list of available activities to choose from is increasing daily, which will be handy when you want to limit the plethora of results that you sometimes get.
As a matter of fact, only the newest 1,000 search results are shown in the portal. If your list is bigger and you want to see all of them, you can download a CSV file from the same page.
You can also filter the results list based on criteria, like user or IP address, but remember that the filter applies only to the list you see in the GUI. If your query was initially limited to the visible 1,000 entries, the actual results list following the filtering might not be complete.
4) Exchange auditing reports
The most common way to examine activity logs for Exchange, even since Microsoft released unified auditing, is to run the Exchange auditing reports. These track administrators’ actions, along with the mailbox activities performed by delegates, admins, or mailbox owners. Admin auditing is enabled by default and monitors everything that admins are doing in the Exchange Admin Center (EAC) or in PowerShell, except the Get, Search and Test cmdlets.
Keep in mind that, in contrast to the admin audit, mailbox audit logging is not enabled by default. You must turn it on for each mailbox, using PowerShell, with this command:
Set-Mailbox <Identity> -AuditEnabled $true
To use Exchange auditing you should open the EAC, go to the Compliance Management page, and select Auditing, where you will find plenty of different options for running your activity reports. Administrators get access to these options by default. If non-admin users (like legal staff or the records manager) need permission to view this content, just add the users to the Records Management role group or assign the Audit Logs role to the user using the Shell.
5) Make the most of alerts
Alerts are the watchdogs of Office 365. Built to target the most encountered and highest-risk security scenarios, they are triggered by set activities to notify administrators to mitigate a threat before it’s too late. Alerts look for mailboxes that gets compromised, suspect file use (like many files being deleted), elevation of privilege, and a multitude of other activities. When a possible risk is found, an alert is fired, and you receive notice by email with details about the threat so you can take action.
Note: To manage activity alerts, make sure you are assigned the Organization Configuration role in the S&CC.
There are two types of alerts that you can set up. Custom alerts are basically audit entries that are set to notify you when they pop up. Elevation of privilege alerts are a default policy in Office 365 that will warn you if the admin privileges have been increased for a user.
Get a grip on your information with auditing
The new unified auditing, improved security alerts, and the old but still powerful Exchange auditing reports combine to increase visibility and awareness inside your enterprise. This has become vital for management and IT as use of Office 365 grows, and together with it, security needs.




