In 2012, Gartner predicted that two-thirds of companies would be using mobile device management (MDM) by 2017. At its core, it is the process where IT administrators configure policies to optimize the security and functionality of mobile devices within their organization. This is achieved through the MDM server’s management console. The policies are then pushed over the cloud to each agent, on each mobile device. In this article, we’ll review some of the features and benefits of MDM and then compare Office 365 to Microsoft Intune.
Key features
Today’s products support a variety of mobile devices, including smart phones, tablets, and even laptops. Features are controlled through APIs. Generally, the solutions offer the following key features:
- Remote data wiping
- Password enforcement
- Data encryption enforcement
- Device tracking
- Device inventory
- App distribution
Why successful companies embrace MDM
For starters, it’s important to keep track of your assets no matter what business you’re in. By utilizing these solutions, organizations can always have up-to-date information on every device, from any location. Second, mobility comes with its own inherent risks—devices can get lost or connect to unsecured networks, potentially exposing your company’s confidential data. As a result, many companies today are investing in MDM solutions to ensure device encryption.
There’s also the fact that it frees the burden of responsibility from the end user by systematizing device management. MDM also improves productivity by allowing employees to simply focus on their work without worrying about getting approval from supervisors or checking whether they’re abiding by organization protocols. With an MDM solution, you can easily comply with any industry, financial, and government regulations without any issues.
On top of all this, MDM caters to a growing mobile workforce. You can still easily collaborate with your remote colleagues—but with the right mobile device policies and software solutions in place. With the popularity of mobile devices and the growth of remote employment, many companies today are making MDM a trending priority.
What to look for in a solution
Once you see the value of implementing an MDM solution, the next step involves determining what types of features make the most sense for your business. While there are many options, an MDM solution will only be beneficial if it aligns with your mobile security goals.
As such, you must thoughtfully evaluate a platform to see if it is the relevant choice for your company’s policies. For instance, what happens to cached data when an employee is terminated? How are business and personal data separated? Note that policies must be first put in place by your organization before you can even begin considering a solution. Here are some essential features to look for as you explore solutions:
- Cloud support
- 24/7 monitoring
- Geofencing
- Passcode enforcement
- Remote monitoring
- Remote configuration
- Functionality restoration
- Jailbreaking alerts
- Scalability
- Compliance reporting
Implement an MDM the right way
When it comes to data breaches and thefts, it’s crucial to balance security and convenience. This starts with understanding the scope of all devices that may have access to, or store, sensitive data. With an MDM solution, devices can be instantly wiped if they are lost or stolen.
In this regard, it is imperative to consider what your company wants. Don’t give users access to every capability just because you can. Think of who needs access to what and how. Only offer specific capabilities to users who need them to successfully perform their duties.
Then, determine how many devices, apps, and users there are throughout your company. With this key information, you can make more prudent decisions.
Next is selecting the right platform for your company. After that, it’s important to continue investing in reliable IT support—you won’t be able to face mobile usage challenges without it.
Explore the legal side
When implementing MDM, you also need to ensure that the solution you’re considering will help you abide by local, state, and federal laws. In many cases, there are no laws that outline the difference between personal information and business data. And lawmakers are still trying to evaluate the legal implications of BYOD and MDM. However, it’s worth noting that the GDPR regulations issue stringent fines to any company that experiences a data breach and has EU residents as customers. This is also something to keep in mind when designing your policy.
There are also gray areas in highly regulated industries such as finance and health care, where federal and state laws have been implemented to define what types of data employees can manage and how they access those data. These laws do not explicitly state the types of information companies are not allowed to manage or control.
When drafting your MDM policy, you should consult an experienced technology expert or lawyer to avoid running into issues down the road, such as an employee suing you for invasion of privacy. It’s also a good idea to inform your employees of your policies when you hire them.
MDM for Office 365 vs Microsoft Intune
In 2015, Microsoft embedded Intune’s MDM capabilities into Office 365. This was great news for clients who already used MDM for Office 365, which is included with an Office 365 subscription. Since Microsoft Intune coexists with MDM for Office 365, you can assign a set of end users for Intune and a set of end users for MDM for Office 365. But there are a few differences.
MDM for Office 365
With this Microsoft MDM option, you have several native MDM capabilities from Exchange ActiveSync (EAS) that let you:
- Manage all mobile devices connected to Exchange Online
- Remotely wipe emails from any device
- Enforce passcode requirements
- Prevent access to emails and documents in alignment with company policies
- Report devices that do not subscribe to the policy
- Access reports on jailbreaking
Plus, MDM for Office 365 utilizes Intune to help deliver these features.
Microsoft Intune
Microsoft Intune is a PC and cloud mobile management platform. Intune lets you:
- Implement full MDM beyond Office 365
- Manage and enroll corporate-owned devices, including traditional PCs
- Manage Linux and UNIX servers
- Use Mobile Application Management to protect customer-built business apps
- Use Office Mobile to protect access to corporate data
- Provide additional security for web browsing
Here’s a table summarizing Microsoft’s two offerings:
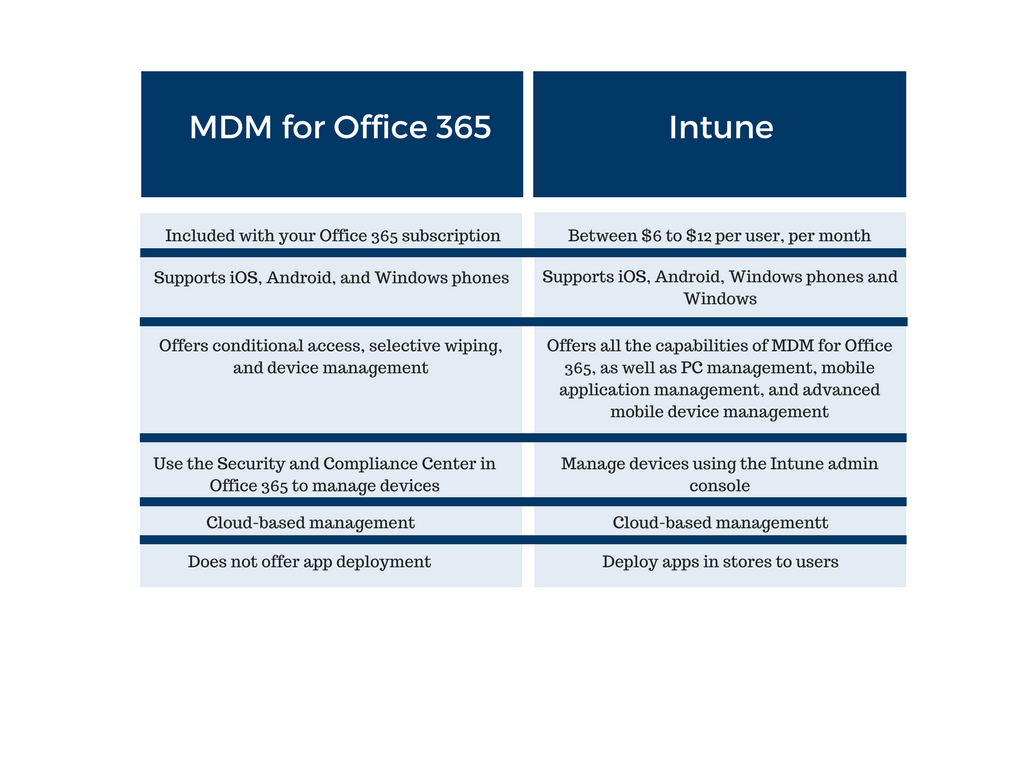
For most SMBs, MDM for Office 365 should be enough. Where Microsoft Intune shines is in its ability to push profiles for Wi-Fi, VPN, and more. Moreover, Microsoft Intune can deploy apps and line-of-business apps in stores to users. It also offers more secure web browsing through the Intune Managed Browser app. In the end, which platform you pick depends on your company’s specific needs and objectives.